5. Avoiding the Pitfalls of Predatory Publishing
Guidance for Graduate Students and Junior Scholars
© 2023 Karin Ardon-Dryer et al., CC BY-NC 4.0 https://doi.org/10.11647/OBP.0364.06
It almost happened to me… has it happened to you?
I was a postdoctoral fellow at the time of this incident, in the process of applying for tenure-track faculty positions. I was feeling the pressure to increase my publication count — I had been told that having more publications would increase my chances for landing the tenure-track position at an R1 institution I so dearly wanted.
At this point in my academic career, truth be told, I had never heard about predatory journals, and had no clue of the potential pitfalls awaiting me as I entered the academic publishing world. That is a large part of why I was so impressed when I was contacted by a journal editor, inviting me to submit a manuscript to a special issue.
Since I had not heard about the journal before, I did do some research: I googled the journal and looked through the website. It seemed like a professional website, and the articles I found seemed okay. I even recognized one author’s name as someone in my field, so I started feeling more confident about the journal. But still, I wanted to make sure I was submitting to a good journal, so I looked up their editorial board and recognized a name or two. I was told there would be a fee for publication but given that I had never submitted (by myself) to an academic journal before, I assumed this was a normal part of the process. So far, everything seemed legitimate, and since the very notion of predatory journals was not something I was aware of yet, I had no remaining suspicions.
As I began working on the manuscript, which was a review of literature relevant to the special issue, I even invited a colleague to coauthor with me — someone who had experience publishing in other academic journals. We finished the manuscript and submitted it to the journal. Mentally, I was prepared to wait months to get a review back, and was merely hoping for a revise and submit, rather than a straight rejection. So, less than twelve hours after submission, I was shocked to see an email from the journal editor. Assuming that only a desk reject would come back that fast, I dejectedly opened the email, preparing myself for the harsh reality of having wasted my time. To my great surprise, it was an acceptance letter, with no suggested revisions, and in fact, no reviewer feedback at all!
This finally raised some red flags for me, and when I discussed this with my coauthor, we both agreed this was strange, and that we should remove our submission. I crafted an email to the journal editor, stating that as it turned out, I did not have the budget to pay the publication fee, so I needed to withdraw my submission. I had hoped this tactic would discourage them from harassing me — surely all they were after was my money, so if I told them I had none they would leave me alone. However, after a little back and forth with the editor, they said they would be willing to waive the fee if I would still just publish the manuscript with them. They were not giving up easily, which was odd. If they were not after my money anymore, what was their end game?
By this time, I had done a bit more research and learned that predatory journals were a thing I needed to guard against, and that this journal had been flagged on some of the predatory journal databases as engaging in less-than-scrupulous activities. I went on the attack and convinced the journal not to publish my manuscript. Luckily, they acquiesced, and I was saved from publishing in a predatory journal. Clearly, though, other scholars have not been so lucky, and to my knowledge, that journal still exists, publishing manuscripts with no peer review, and charging authors for non-existent services. While the journal’s willingness to waive the fee places them in a grey area, the fact that they claimed to do the peer review, but then did not, makes them a direct threat to the credibility of scientific knowledge production.
Since that near miss with publishing in a predatory journal, I am extremely cautious about where I submit my manuscripts. I receive similar solicitation emails daily, as do all my colleagues. We have become accustomed to deleting them, barely letting them register in our minds now. I use a range of tools and critical thinking exercises to vet journals — many of which are outlined in the following chapter. Luckily, I avoided having my scholarly reputation ruined, because had that manuscript been published, I would have always had to explain it — removing the publication from my CV would have been unethical, yet any scholar who knew the field would have questioned the quality of my publications if they saw I published in that journal. This is a situation too many junior scholars now find themselves in.
It is my hope that my experience, and the tools I present in this chapter, will help others stay safe from the growing pitfalls of predatory publishers in the academic publishing world.
Introduction
Publishing in peer-reviewed scientific journals is the cornerstone of academic assessment and crucial for the communication of research findings (Christopher and Young 2015). In recent years, hundreds of thousands of researchers worldwide from research institutes, universities, and federal authorities published their papers in predatory (pseudo-scientific) journals (Boucherie 2018). This number includes researchers from even the most prestigious institutions, such as Harvard University (Clark 2018) and even a Nobel laureate (Boucherie 2018). While the problem is global (Beall 2016), some geographical regions are more prone to being targeted than others. (See Chapters 2 and 3 in this book for more detail.)
As explained in other chapters, controversy still surrounds the term predatory and how to define it. Nonetheless, there is some consensus on the practices that authors should be aware of as possible indicators that a journal is not trustworthy. For instance, authors should be suspicious of journals that offer quick acceptance times and cheap publishing fees that are not transparently explained in the submission guidelines. As revealed in the Bohannon hoax highlighted in Chapter 4, authors should be concerned if they receive an acceptance letter — and an unexpected invoice — from the publisher. Authors should also be aware of journals that do not provide peer review (Roberts 2016) or provide fake reviewer reports (Bowman and Wallace 2018), as in the example of two authors who submitted a manuscript to a predatory journal with only a repeated sentence containing expletives demanding they be taken off the journal’s mailing list — and received an immediate and enthusiastic acceptance (Brezgov 2019). Finally, authors should be leery of journals that are not indexed in databases such as PubMed, do not conduct copyediting or other publication services, and do not have an archival plan to ensure the article is preserved in perpetuity as part of the published record (Roberts 2016).
Unfortunately, many researchers who submit papers to predatory journals fail to realize they are counterfeit journals until it is too late. In some cases when authors discover their error and seek to withdraw their papers, they cannot (Berisha Qehaja 2020), or else they do succeed, but only after a long struggle, or they are forced to pay a withdrawal fee (Leung and others 2020).
Predatory journals are a real threat to the credibility of science (Manca and others 2019). Students who lack the experience and credentials to recognize predatory journals may also be exposed to information published in predatory journals that may harm their education (Schira and Hurst 2019). Authors do not always understand the negative consequences of publishing their research in predatory journals, which may include consequences such as the loss of the manuscript, negatively scarring their publication records, and damaging their career (Al-Khatib 2016; Grudniewicz and others 2019; Teixeira Da Silva 2013). One of the interviewees in our study discussed the possible ramifications of publishing in a predatory journal: ‘I think it reduces your credibility as a scholar […] it can be sometimes even be hurtful to your career to publish in such journals’ (P02).1, 2 Previous research suggests that those who publish their work in predatory journals and who are impacted the most are early-career researchers, including graduate students (master’s and PhD students) and junior scholars (postdoctoral or pretenure faculty) (Darbyshire 2018; Larkin 2018).
This chapter combines the voices of participants in our interview study with the existing scholarly and mainstream literature to define some of the biggest pitfalls junior scholars and graduate students may encounter as they begin trying to publish manuscripts in the current academic publishing environment. Regarding graduate students, different training and funding models exist across departments and universities, and, as we demonstrate in this chapter, these models can impact graduate students’ experiences with scholarly publishing and the type of mentoring they receive. For example, when a graduate student is accepted to a university and department they may be accepted and receive payment as a Research Assistant (RA), meaning they are fully committed to a known research project, based on a grant or budget their advisor has already obtained. Other students may be accepted as Teaching Assistants (TAs), meaning they are required to teach in their department in addition to performing their research. In some cases, when graduate students start their degree, they already have a designated advisor and a known research project. In other cases, students are accepted to programs or departments without an identified advisor or research topic, which they then select after the first year or two. In some institutions, graduate students are accepted to programs or departments without any financial support for their graduate degrees. Students may also be accepted to programs or departments with a fellowship that will support them; in many of these cases, the research project and identification of an advisor will be made in advance. In some institutions, publication in a peer-reviewed journal is a requirement for receiving a doctoral degree. All these factors influence the nature of mentoring that a graduate student receives and, ultimately, their experience with publishing as a junior scholar.
Awareness of the Problem
Previous research suggests a lack of awareness among early-career researchers regarding predatory journals and the impact they might have. Lack of experience and knowledge to tell the difference between legitimate peer-reviewed journals and predatory journals (Christopher and Young 2015), along with the lack of formal institutional policies and intense pressure to publish, are suggested as the primary reasons why so many early-career researchers publish their work in predatory journals (Al-Khatib 2016). Therefore, there is a great need to raise awareness about the importance of selecting the right journals for publication, especially for young researchers who are in the early stages of building their academic careers (Kurt 2018). Echoing this previous research, many of our participants agreed there is a lack of awareness of predatory journals among early-career researchers, sharing comments such as, ‘many students say they’re not aware of [predatory publishing]’ (P05) or ‘when I started to write publications, I was not aware of how to do it, or where to publish. Some time I just rely on the journals of my classmate, where they publish […] So I don’t I didn’t have like the idea to go and search for this feature journal of my area’ (P03). Another participant noted that predatory journals actively look for ways to deceive inexperienced authors, such as using real people’s names for their editorial board without their permission (P21). One of the ways authors are told to vet journals is to look at the editorial board, but if predatory journals are actively lying about their editorial board, then this seemingly straightforward way of determining a journal’s credibility suddenly becomes much more difficult.
The Role of Mentors/Advisors
Academics involved in the mentoring process should warn and advise early-career researchers on where to submit their manuscripts for publication (Berisha Qehaja 2020). Therefore, research faculty in mentoring roles are the key to the future of science, as they are one of the most important influences on early-career researchers (Bankston 2017). An effective mentor-mentee relationship enhances the mentee’s career and professional development (Ellis 1992; Gaff 2002; O’Neil and Wrightsman 2001), presents more academic opportunities (Busch 1985; Petrie and Wohlgemuth 1994; Wilde and Schau 2014), and can even develop into a more equal colleague-to-colleague relationship (Schlosser and others 2011). Therefore, the presence of an effective mentor for graduate students and junior scholars is an important aspect of their success and education (Foss and Foss 2008). A great mentor influence can be life-changing when ethics, drive, and skills for teaching and research are shared (Wrench and Punyanunt 2004).
Unfortunately, some graduate students and junior scholars may not get proper advice from their direct advisor or mentor and, in extreme cases, may not have any interaction with them at all. Even when there is a designated advisor or mentor, there could be a mismatch between the mentor and the mentee due to personality, communication style, relationship preference as well as career stage, and interest differences (Johnson and Huwe 2002). In addition, not all advisory relationships entail mentoring (Schlosser and others 2011), and not all advisors are relationally competent for the role (Johnson and Huwe 2002).
Suggestions for Improving Mentoring
According to Christopher and Young (2015), educational goals for early-career researchers, whether obtained through formal workshops or less formal mentoring, should include the following: (1) increased awareness of predatory journals, (2) ability to distinguish between legitimate and illegitimate open access journals, (3) understanding the similarities and differences between open access and subscription-based journals, (4) learning to evaluate journals and their processes, and (5) learning how to select the best journal for the scientific study.
Through mentorship and training programs, early-career researchers may be formally or informally educated on basic research concepts, including statistical methods, navigation of the institutional review board, and experience with the peer-review process through research conference presentations and publication (Leung and others 2020). Along these lines, one of our interview participants, a librarian from Africa who now works in the US, suggested bringing students into the research process early, encouraging them ‘to look at the topic that are you working on, what journals that you find that fits this topic, […] so you offer advisory services to them, and guidance and direction on how to publish’ (P02). This corroborates other scholarly work that argues for the importance of educating early-career researchers on how to critically evaluate articles to help them avoid predatory journals and discern between legitimate open access publishers and predatory journals. This kind of training helps to safeguard the process of knowledge production (Christopher and Young 2015; Leung and others 2020). Furthermore, the mentor often guides the submission process by selecting the first and second target journals for submission, or providing lists of acceptable journals, as was shared by some of our participants when they noted things like, ‘there are certain lists of journals that our promotion and tenure committee gave us’ (P02), and ‘my supervisor […] had a list of journals that he recommended’ (P10).
In some cases, the early-career trainee may be solely responsible for assessing a journal’s submission requirements, gathering coauthor conflict of interest forms, creating a cover letter, and submitting the manuscript. However, trainees may unknowingly submit a manuscript to a predatory journal, resulting in consequences ranging from the simple loss of time to the loss of the manuscript and/or data, and in even more extreme cases, the loss of professional credibility. Therefore, it is important to mentor the trainees to educate them about predatory journals and their strategies and ensure proper manuscript submission (Leung and others 2020).
Institutional Differences in Mentoring and Publishing Expectations
Most junior scholars, especially graduate students and postdoctoral fellows, will have a faculty advisor with whom they will work directly. However, in some cases, mentoring may occur from other junior scholars, with no formal advising or mentoring. Mentoring also varies for pretenure faculty. In some cases, the department might assign a senior faculty member as a mentor as part of the tenure process, but often there is little oversight or accountability in the mentoring process.
In addition to vast institutional differences in mentoring, the path to tenure also varies greatly from institution to institution, which has direct implications on the research and publishing requirements for junior scholars (see Table 5.1), depending on whether they are at a research or teaching-focused institution.
Table 5.1 Differences in tenure track process (Research vs. Teaching Institutions) © STEPP Research Team
Early-career researchers, including graduate students, postdoctoral fellows, and junior scholars, are expected to publish their research results as scientific papers to prove their research commitment and to achieve certain academic titles in higher education institutions (Berisha Qehaja 2020), and are therefore more likely to become victims of predatory journals and publishers (Al-Khatib 2016).
Junior faculty feel the pressure to meet their institutions’ promotion and tenure requirements under the ‘publish or perish’ mantra, meaning they feel pressured to rapidly increase both the number of their publications as well as the visibility of those articles (Al-Khatib 2016). Along these lines, a North American scholar we interviewed suggested the push for greater publishing numbers has increased in recent years, ‘I’d say in the last ten years or so, there’s been more emphasis on publishing’ (P05), which may be driving the dramatic rise in the number of predatory journals trying to capitalize on this trend.
There is also pressure on graduate students, from different academic fields, to publish their work as part of their degree completion or long-term career success (Leung and others 2020), a notion corroborated by several of our interviewees, and exemplified by one European participant with decades of international publication experience: ‘in many places it is expected that you publish paper before graduating’ (P18). For example, Mills and Inouye (2021) mention that a master’s student who needs a publication quickly to graduate or apply for an academic post might make a different choice at a subsequent career stage. There is insufficient attention to the processual dimensions of publishing across an academic career and the timing of individual choices in most accounts of predation (Mills and Inouye 2021). The following anecdote from an experienced scholar from Africa drives home the point that young, inexperienced researchers who are scrambling to get publications to find jobs may not fully understand the ethical (and career) ramifications of submitting their manuscripts to any journal that will take them:
As a PhD at my university you need to publish two articles [before you can graduate]. So when you finish your work and […] you submit […] it is rejected, rejected […] rejected. By that time […] the student don’t have too much time to wait. So they just find a journal and pay maybe $100 or $200 and publish it in one or two months. This is really common. Really common. Not because the work is not good […] it is because they don’t have too much time to wait for it. Because good journals sometime take time. Yes. And those who do their work, who have their own idea for their PhD work or their research work in [my country] sometimes face rejection with publication because the equipment sometimes it’s not up to date. And […] a good journal, they need publication with good equipment or up-to-date equipment. So, by this time […] after a lot of rejection, people will just rely in predatory journal […] knowing that they are predatory journal and they say, okay, I just want to finish and then I’ll find time to do something good after. (P03)
As this quote illustrates, one of the biggest problems with predatory journals is that they take advantage of early-career researchers’ desire to share their work; they bombard them with emails to invite them to submit a manuscript, attend a conference or become an editorial board member for a journal.
The desire to have your work be recognized by the field as important or impactful is a powerful drive for many researchers, as exemplified by interview participants who discussed the feelings they experienced when they began receiving solicitation emails early in their careers. A North American librarian surmised:
[…] when you see a journal come up in your email, that’s like, we here at the-journal-of-this-actually-sounds-very-reasonable-study says, ‘You can publish with us and we’ll get your work out there.’ I can see how that is very tempting and it’s probably very easy to get confused [when] those websites probably look exactly the same […] and it’s hard because you want the praise and you want to be told that your work is good. But […] Yeah, it’s absolutely a scam. And I have seen our own librarians fall for it (P07).
A South American academic researcher confirmed the widespread occurrence of receiving solicitations from suspicious publications, saying ‘professors here and all over the world, it’s not different here in [my country], we usually receive many invitations. The invitations are very strange because sometimes the English is not very good and they invite you to publish in journals that is nothing to do with your field’ (P13). She continued her anecdote by noting she makes a point to share suspicious solicitations with her students, and to warn them not to fall prey once they defend their thesis, pointing out that publishers have mechanisms to find and target inexperienced researchers who may be the most desperate for publications as they enter the academic work force.
As these examples illustrate, for graduate students and junior scholars, getting these emails may seem like a great honor, but in many cases, these are sent by predatory journals and could lead to disastrous outcomes if a manuscript is submitted to one of these nefarious publications (Bowman and Wallace 2018; Roberts 2016; Wood and Krasowski 2020). Kurt (2018) stated that the pressure on early-career researchers to publish often causes them to fall prey to advertising used by predatory journals because they do not analyze the quality of the journal before sending the manuscript. Unfortunately, what many early-stage researchers do not understand is that when their work is published in a predatory journal, it not only condemns their work to obscurity, but also damages their reputation, academic credibility, and careers (Bowman and Wallace 2018; Darbyshire 2018). Additionally, the article they submitted has little or no validity, might not even be published at all, or it might be posted on a low-visibility site (Bowman and Wallace 2018).
Strategies for Avoiding Predatory Journals
The most important thing before submission of a manuscript is to educate yourself (or your students) about the journal. Knowing your field and taking the time to research a journal before submitting is key to avoiding predatory journals (Roberts 2016). The following sections provide insights into some additional strategies and resources to avoid falling prey to a predatory publisher and losing your work. Most of these strategies and resources have been addressed in scholarly literature, but we also supplement the findings of previous literature with insights from our interviewees, as appropriate. While some of the strategies listed below are rather straightforward (e.g., examining the journal scope and assessing the technical quality of the journal website), other strategies require more critical thinking and subjective judgement (e.g., knowing your field or determining the quality of individual articles), along with other strategies that may seem straightforward initially, but actually require critical thought (e.g., examining the editorial board, checking indexing sites and impact factors, or determining if a journal is known to colleagues). Although the mechanisms discussed in the following sections are not exhaustive, they do represent a series of indicators that can help authors determine whether a journal is legitimate or predatory.
Scope of the Journal
Shamseer and others (2017) note that an overly broad scope for a journal could be a warning signal, an indicator also used by our interview participants. For example, a North American librarian noted she examines ‘whether or not what they claim the journal is matches what they’ve said they want my article for’ (P04). Another participant, also located in North America, shared how he considers whether ‘they have a focus in a certain field, or they just kind of like scattered?’ (P08). Thus, paying attention to the declared scope of a journal and ensuring the articles they publish match that scope is one mechanism of determining credibility.
Technical Quality
Although Beall (2015) lists ‘poorly maintained websites’ (p. 5) as one of the features that could indicate a predatory journal, this criterion has also been called into question because it could place newer journals, or those being established in non-English-speaking countries, at a disadvantage and make it harder for them to break into the mainstream publishing area (Memon and Waqas 2018). Therefore, a careful look at several technical aspects of a journal may help establish whether it is a predatory journal, or just a startup publication that has not yet worked out all the errors and bugs in their website. Our interview participants offered several ways to examine the technical quality of a journal’s website that may help determine its credibility. Clear statements of policies were one of the main components our interview participants pointed toward as a way to vet a journal (P03, P07), as exemplified by a South American senior researcher who argued that if ‘the journal does not have explicit criteria and clear editorial policies’ (P13), it could be a warning signal of predatory activity, especially if you ‘can’t tell where it’s based […or] if you can tell where it’s based is different to where they claim it’s based’ (P09). On a more general level, a European publishing professional suggested taking a broader look at the digital presentation, and ask questions such as, ‘Does the website look like a total mess? Is it full of stock photos? These kind of things. I’ve done this kind of analysis myself’ (P09). Therefore, taking a critical look at the technical aspects of a journal’s webpage can be an important aspect of the vetting process.
Know Your Field
Knowing your field will help researchers to select a journal that is topic-appropriate, within the scope of their research, respected among other researchers in their disciplines, and widely indexed and accessible to readers (Bowman and Wallace 2018; Christopher and Young 2015). Yet this is easier said than done, based on interview comments such as this one from a North American academic researcher who noted, ‘you kinda have to have some expertise in the field to figure out if a journal is predatory’ (P08). One way to begin acquiring this expertise is to talk to colleagues to make sure they have heard about the selected journal, and ask yourself questions such as, ‘Do you know anyone who’s published there? Do you actually read this journal? Would you cite the articles in this journal yourself?’ (P09). It is also important to keep in mind that some predatory journals use similar names as legitimate journals. Thus, authors should examine any publication in question carefully and exercise caution before submitting to an unfamiliar journal (Bowman and Wallace 2018), and do not ‘just go for journals that tell you they’re going to give you a quick publication’ (P23), as this can be a warning sign of predatory practices (and less-than-rigorous peer review).
Quality of Published Articles
One of the trickier mechanisms to detect whether a journal could be predatory is to examine the quality of the published articles. The quality of published articles is not always listed as a potential strategy for identifying predatory journals in the scholarly literature (e.g., Shamseer and others 2017) or from organizations aimed at assisting authors (e.g., Think. Check. Submit.), yet several of our participants indicated this was a component they examine when selecting a journal, as exemplified by the narrative shared by a North American researcher who regularly taught graduate students how to navigate academic publishing:
[…] there’s journals where I thought about publishing. And I’ll pull a few sample papers from the journal, and […] if I read it and I’m like, wow, this thing has some gaping holes in it, you know it looks like the editing is not careful […] they just leave out blatantly obvious things like that and I’m like okay that’s junk. Yeah, I’m not gonna publish there. So, that’s a judgment call, that’s not just charging a fee. (P08)
Therefore, examining individual articles from a journal can be a way to begin critically examining whether or not the journal seems to be vetting individual research and providing the expected services of peer review and copy editing.
Editorial Board
One of the strategies that some resources suggest for vetting a journal is to look at its editorial board (e.g., Shamseer and others 2017; Yucha 2014). However, this strategy has its limitations because, as predatory journals have grown more sophisticated in their deception, one of their tactics is to list individuals on their editorial board without their knowledge or consent (Ruiter-Lopez and others 2019). Despite the growing acknowledgement that editorial boards are relatively easy to fake, many of our interview participants suggested a good way to determine journal credibility was to ‘look at the editorial board’ (P23) and that ‘if they recognize universities or the people who are on those boards, that’s probably a sign that that journal is legitimate, generally speaking’ (P07).
These recommendations, however, must now be couched with a caveat to look further than just whether prominent scholars are listed on the editorial board. For example, if there are other warning signals present when examining the journal, it would behoove the potential author to reach out to one or two of the editorial board members and ask them about the journal.
Indexing and Impact Factors
Checking whether a journal is indexed in a reputable database, along with assessing the impact factor of the journal through a credible external source (do not just trust what the journal says — stating false impact factors is now a common tool used by some predatory publishers) can be a good tool for vetting journals (Shrestha and others 2019). Despite some academic researchers and librarians viewing an overreliance on impact factors as a challenge to research quality (see Chapter 3), checking indexing (e.g., P04, P09, P13, P18) and impact factors (e.g., P09, P23) were some of the most common mechanisms mentioned by our interview participants as a way to determine whether or not a journal was credible.
In other cases, authors thought using an indexed list like PubMed Central® would be a good choice, but indexing does not guarantee that a given journal is legitimate (Misra and others 2017). The caveat to the reliability of some indexing mechanisms was addressed by one European researcher with decades of publishing experience who noted:
Anybody can sign up for Crossref and the DOIs are given. So you’ll find that all predatory journals have ISSNs and have DOIs. They might not be in ISI, but some other people are more careful. They won’t be properly indexed, probably. There are exceptions. Some get into World of Science and also to Scopus, but not so many, but basically they can’t usually get in properly indexed. [There are] all sorts of extraordinary organizations […] Copernicus is one […] (P18)
The Copernicus Indexing service, as mentioned by this interview participant, is one among a growing number of services that has contributed to the difficult terrain researchers must navigate as they prepare to submit their research for publication. Simply believing the journal or publisher when they list indices they are included on, or because they tout an impact factor, is no longer a valid method of vetting journals — one must also vet the index and impact rating organization to ensure they are not also promoting predatory journals.
Known to Colleagues
Another mechanism for vetting the credibility of journals mentioned by our interview participants was asking whether the journal was familiar to colleagues in the field. A North American Librarian suggested, ‘doing a lateral reading about the journal […] Can I Google it and find a real journal? What do other people say about that journal?’ (P07) and a European publishing consultant concurred, suggesting inexperienced authors should ‘look at whether people that you know in your subject area, or that you respect, or that are leaders in your area are publishing in that journal’ (P23). While the mechanism of checking with colleagues can help steer junior researchers toward credible journals, there are constantly new journals (which may be entirely legitimate and credible) being added to each field, so simply asking colleagues who may not be up to date on the latest journal developments should be augmented with other vetting strategies.
Tools to Aid the Avoidance of Predatory Journals
As the diversity of strategies listed above indicate, it is becoming more and more complex to independently verify whether a journal is predatory or not. In response, several types of tools have been developed to help authors navigate the increasingly savvy attempts of predatory journals to lure authors into submitting their manuscripts. The anecdote below, shared by a publishing consultant working in eastern Europe, highlights the extent some predatory publishers go to deceive authors and exemplifies the need for additional tools to help avoid the ethical pitfalls of predatory publishing:
If I was starting a predatory journal […] I would pick a name that was similar to a journal in my field that was already well-known, so rather than Annual Reviews of Ecology and Systematics, I might call my journal Annual Reviews of Systematics and Ecology. Make a website that looks quite similar to the reputable one, and this is happening. It happens all of the time. There are millions of examples of this, especially in medical fields. I would put together an editorial board. I wouldn’t necessarily even tell people that they were on the editorial board. This happens all of the time as well. Get some well-known names, put them on the website, and market that. Get some people to submit papers and keep the APC down so you can publish with us for $800 rather than $1500. Quick publication, the product looks good, but it’s all about the money, and this is happening all of the time. There’s millions of such journals. (P23)
In the increasingly deceptive environment of academic publishing, mentors and faculty in charge of training graduate students should be aware of the numerous tools available to help vet journals. There are three main types of tools available to help authors determine if a journal is predatory: watchlists (previously called blacklists), safelists (previously called whitelists),3 and checklists.
Watchlists & Safelists
As detailed in earlier chapters, identification of potential predatory journals started in 2008 when Jeffrey Beall, a librarian at the University of Colorado Denver, created Beall’s List, which contained a handful of journals and publishers that Beall identified as predatory (Beall 2012). The list, which was officially published in 2010, named ‘potential, possible, or probable predatory scholarly open access publishers’ (Quek and Teo 2018: 3). In 2017, due to legal pressure and increasing scrutiny about the methodology used for journal inclusion, Beall’s List was taken offline. However, archived versions of the list are still available on the web, and these are supposedly being updated by scholars who wish to remain anonymous (e.g., ‘Contact’ [n.d.]). Cabells Blacklist, now renamed Cabells Scholarly Analytics, is another example of a watchlist. Although Beall’s List was free of charge, access to Cabells list requires payment, which makes it unattainable for most individual scholars (unless their institutions purchase a subscription). Additionally, both scholars and institutions have begun to realize that, due to the ever-changing landscape of predatory journals, watchlists are outdated almost as soon as they are published, making them an unreliable source for vetting journals (Koerber and others 2020; Neylon 2017).
An alternative to watchlists is safelists — or lists that provide names of presumed legitimate journals that meet certain quality criteria (Umlauf and Mochizuki 2018). Examples of safelists include Web of Science (WoS), Scopus databases, Directory of Open Access Journals (DOAJ), and many others (Koerber and others 2020). Although these watchlists or safelists might be helpful in some cases, new predatory journals will not appear on them, or the predatory journals might change their names and publishers. Therefore, some studies (e.g., Koerber and others 2020; Manca and others 2019) question the effectiveness of these lists. The issues with maintaining an updated watchlist or safelist were acknowledged by some of our interviewees. For example, an Asian publishing professional noted that ‘not all predatory journals are on the blacklists’ (P27), and a South American researcher shared that she is ‘very careful when [using] a list […] because I think there are mistakes in this list’ (P13).
Additionally, some fields, institutions, or even countries provide their own lists of vetted journals. China and India were two specific countries listed by our participants (P17, P19, P23) where national lists were in place, and a Southeast Asian scholar (P39) indicated that his institution had an approved list of journals for his field.
Checklists
As an alternative to watchlists and safelists, a growing trend has been for scholars and institutions to develop checklists that can help authors determine whether a journal is predatory. For example, Rele and others (2017) created a checklist that authors could use to evaluate a journal and guided authors on how to consider specific criteria when evaluating a certain journal. These authors’ recommendations include two steps: evaluation of the journal and evaluation of the publisher, where the total scores at the end of the evaluation will define whether the journal is a proper choice or not for publishing the work. Evaluation of the journal requires searching the internet for the journal name, then looking for the following content on the journal’s webpage: editorial board, the review process, conflict of interest statements, revenue sources, archiving policies or procedures, publishing schedule, author fees, copyright information, indexing inclusion, access to past published articles, and information on the number of articles published by the journal. The second evaluation step includes a web search for the publisher and information about the publisher.
Some scholars have also taken a more field-specific approach to developing checklists. For example, Shamseer and others (2017) demonstrate that potential predatory journals may be distinct in some key areas from presumed legitimate journals and provides evidence of how they differ within the biomedical fields. The key points described by Shamseer and others (2017) are summarized below, and could be used as an author checklist for determining the credibility of a given journal, especially in the biomedical fields:
The scope of interest includes non-biomedical subjects alongside biomedical topics.
- The website contains spelling and grammar errors.
- Images are distorted/fuzzy, intended to look like something they are not, or are unauthorized.
- The homepage language targets authors.
- The Index Copernicus Value is promoted on the website.
- Description of the manuscript-handling process is lacking.
- Manuscripts are requested to be submitted via email.
- Rapid publication is promised.
- There is no retraction policy.
- Information on whether and how journal content will be digitally reserved is absent.
- The Article processing/publication charge is very low (e.g., $150 USD).
- Journals claiming to be open access either retain the copyright of published research or fail to mention copyright.
- The contact email address is not affiliated to a professional organization or to the journal (e.g., @gmail.com or @yahoo.com).
Although Shamseer and others (2017) recognize that these criteria are likely not sensitive enough to detect all potentially illegitimate, predatory journals, they feel they are a good starting point.
One of the most widely used and acknowledged checklist tools is Think. Check. Submit., which was established by scientific societies and publishers to guide authors through the publishing process (Grudniewicz and others 2019). Think. Check. Submit. provides simple guidelines that authors can use to assess a journal or publisher before submitting an article and was one of the most common tools mentioned by our interview participants (e.g., P09, P21, P23, P44). For example, using these tools, authors can distinguish between a predatory journal and a new journal that follows the principles and standards of ethical scientific publishing but has not built up its reputation yet (Larkin 2018). The key questions posed by Think. Check. Submit. are listed in Table 5.2.
Table 5.2 Evaluation Questions for Vetting Journals
We created an additional tool following the Think. Check. Submit. tool. Our method does not require authors to be familiar with any existing list. Authors could follow questions that are similar to those mentioned above and will help provide an in-depth investigation of a questionable journal (See Figure 5.1).
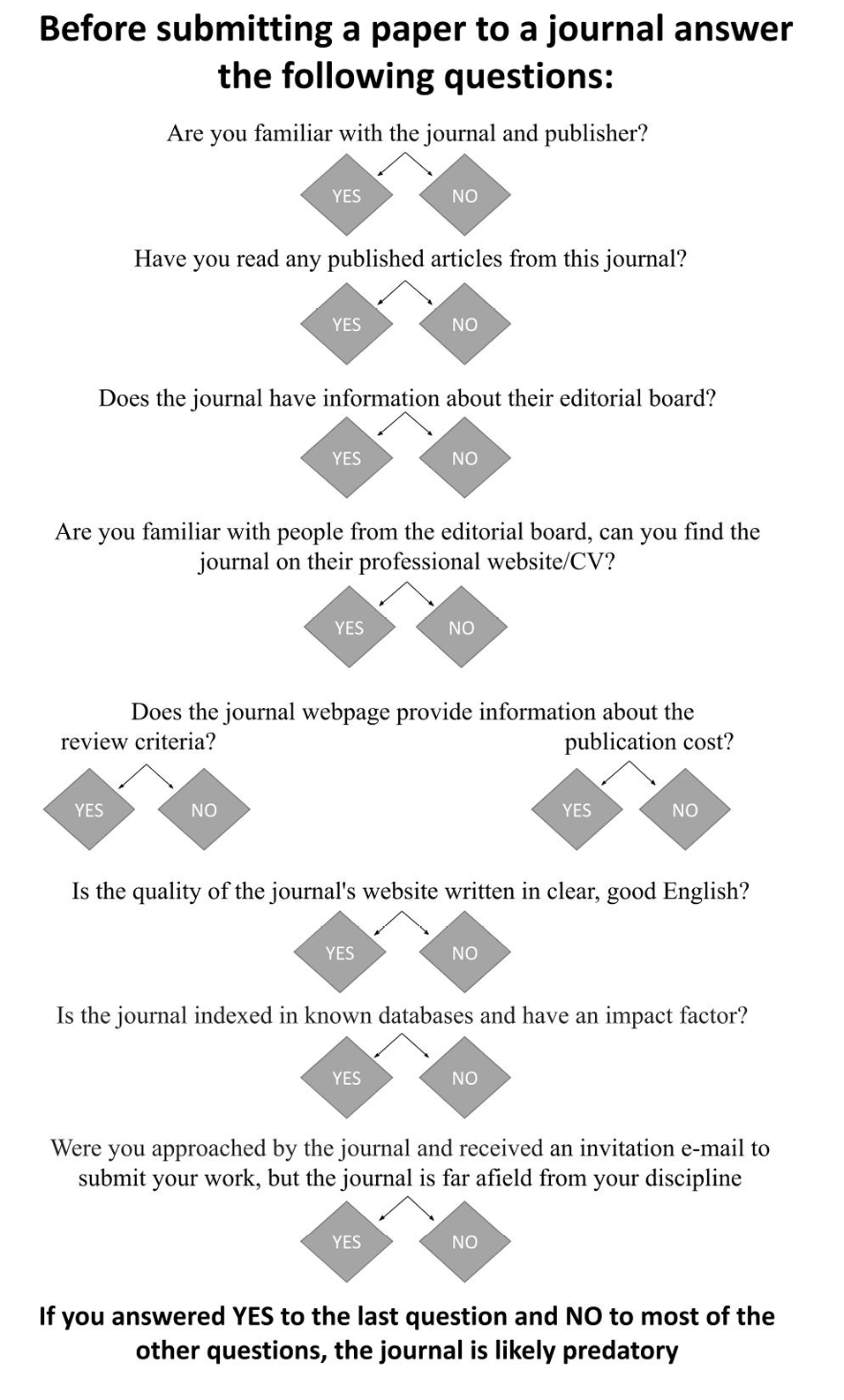
Fig. 5.1 Karin Ardon-Dryer. Before submitting a paper to a journal, answer the following questions (2022). © STEPP Research Team
Publishing in peer-reviewed scientific journals is the cornerstone of academic assessment and is crucial for the development of early-career researchers, including graduate students, postdoctoral fellows, and pretenure or junior faculty. Publishing papers in predatory journals, a common misstep among early-career researchers, could result in a series of negative consequences, such as the loss of the manuscript, negatively scarring the scholar’s publication record, and even damaging the scholar’s ability to be hired at certain institutions. Unfortunately, many of those who submit papers to predatory journals fail to realize the potential consequences until it is too late. Some of the issues come from the fact there is not enough awareness and experience among early-career researchers regarding predatory journals and the impact they might have. Advisors, mentors, and senior faculty have an important position in educating and providing guidance to early-career researchers. This chapter provides information mentors could use to guide graduate students and junior scholars to make sure they avoid the pitfalls of predatory publishing.
Key Takeaways
- Publishing in peer-reviewed journals is a crucial part of career development for faculty with research-related duties.
- In recent years, researchers at all stages in their careers, in all disciplines, and from countries in every region have fallen prey to predatory publishers, although graduate students and early-career faculty may be especially susceptible to falling prey to predatory publishers.
- While the term ‘predatory’ is somewhat controversial, there are certain markers that are broadly agreed upon which indicate less-than-ethical publication practices.
- Typically, once an author realizes they have submitted their work to a predatory publisher, it is too late to recover their work, and may damage their professional reputation.
- The range of institutional expectations and support for graduate students and early-career faculty means the levels of exposure and training related to ethical research practices and potential pitfalls varies greatly from institution to institution and even from department to department.
- Previous research suggests a lack of awareness among early-career researchers regarding predatory journals and the impact they might have.
- The role of mentors and advisors is crucial in educating graduate students and early-career faculty about the potential pitfalls of predatory publishing.
- The pressure to publish for early-career faculty and graduate students may contribute to the increasing trend of submissions to predatory journals, which often tout quick publication times and do not offer robust peer reviews.
- Three main tools are widely available to help determine if a journal is predatory: watchlists, safelists, and checklists.
- Numerous strategies can be used to help detect and avoid predatory journals, including the following: examining the scope of the journal, reviewing the technical quality and accuracy of their digital footprint, knowing the journals and researchers in your field, critiquing the quality of a journal’s published articles, researching the editorial board, vetting claimed indexing and impact factor data, and determining whether a specific journal is known to your colleagues.
Discussion Questions
- Have you or anyone you know fallen prey to a predatory journal? If not, discuss how you have avoided the pitfalls. If yes, discuss how you were deceived and what can be done to avoid it again.
- Discuss some reasons why junior scholars, and especially PhD students who have publication requirements attached to their degree, might turn to predatory publishing.
- Were you aware of predatory publishing before reading this book/chapter? If so, where did you hear about it?
- Discuss the strategies in the chapter to help avoid predatory publishing. Have you used any of these strategies? Do you feel there are certain strategies you might use more than others? Why?
- Examine some of the tools used to detect predatory publishers. Is there a different tool suggested or used in your institution/department? Do you feel a certain tool is more effective than others? Why?
Journal Assessment Activity
The purpose of this activity is to help junior researchers determine the quality of journals in their field. Assessment of the journal will be based on two factors: the quality of the journal itself, and the content of specific articles.
STEP 1: Divide the participants into groups of 2–4 people.
STEP 2: Each group will identify 5 journals in their field. They should attempt to find journals that range in quality.
- Evaluate each of the journals to determine which ones are questionable and which ones are legitimate. Rank the journals as one of the following categories:
- Predatory
- Questionable
- Legitimate
- Ask the group to list resources they used, and any other strategies they used to evaluate the journals.
NOTE: As a time-saving measure, the instructor may wish to find journals they feel fall into each of the above categories and begin the activity at STEP 3.
STEP 3: Have each group select one article from each identified journal. Then, have the groups exchange articles. The groups should then evaluate whether the articles come from predatory, questionable, or legitimate journals.
Use the provided worksheet to help facilitate the discussion afterward.
STEP 4: Have the groups share their assessment of the journals, based on the articles they reviewed. See if the different groups assessed the journals the same, or differently, and why that might be.
STEP 5: Show them the Think. Check. Submit. website: https://thinkchecksubmit.org/journals/
- Discuss whether they used some of those same strategies.
- If time permits, have them reevaluate the journals based on the Think. Check. Submit. rubric and see if they come up with the same journal categorization.
Discussion Questions
- How confident do you feel determining which journals/articles are legitimate/predatory?
- What factors helped you feel this way?
- What is the main thing you learned from this exercise?
- What is the first thing you might check the next time you are trying to determine whether or not a journal is credible?
Journal Assessment Worksheet
INSTRUCTIONS: Please use this worksheet to record the thought process of the group. It is NOT necessary to reach a consensus. Rather, note how many people felt the article met the criteria for each question and list a couple of reasons. (Example: 3 felt the journal was high quality because [reason 1] and [reason 2].)
The facilitator will screen share this document so everyone can see the responses as they are being entered to ensure the worksheet is correctly capturing your assessment of each of the articles.
|
ARTICLE 1: [please fill in title of first article assigned to you] |
|
How would you assess the quality of this article? [high, medium, or low] |
|
How would you assess the quality of the journal in which this article is published? [high, medium, or low] |
|
Do you think this article is published in a predatory journal? [yes or no] |
|
What are the factors you considered in responding to each of the questions above? |
|
ARTICLE 2: [please fill in title of second article assigned to you] |
|
How would you assess the quality of this article? [high, medium, or low] |
|
How would you assess the quality of the journal in which this article is published? [high, medium, or low] |
|
Do you think this article is published in a predatory journal? [yes or no] |
|
What are the factors you considered in responding to each of the questions above? |
References
Al-Khatib, Aceil. 2016. ‘Protecting Authors from Predatory Journals and Publishers’, Publishing Research Quarterly, 32.4: 281–85, https://doi.org/10.1007/S12109-016-9474-3
Bankston, Adriana. 2017. ‘Needed: Flexible Mentors in Science’, Inside Higher Ed, https://www.insidehighered.com/advice/2017/05/01/advice-how-research-scientists-can-best-mentor-those-who-work-their-labs-essay
Beall, Jeffrey. 2012. ‘Predatory Publishers Are Corrupting Open Access’, Nature, 489.7415: 179, https://doi.org/10.1038/489179a
——. 2015. ‘Criteria for Determining Predatory Open-Access Publishers’, Scholarly Open Access, https://crescent.education/wp-content/uploads/2017/09/Criteria.pdf
——. 2016. ‘Essential Information about Predatory Publishers and Journals’, International Higher Education, 86, https://doi.org/10.6017/IHE.2016.86.9358
Berisha Qehaja, Albana. 2020. ‘Avoiding Publishing in Predatory Journals: An Evaluation Algorithm’, ERIES Journal, 13.3: 154–63, https://doi.org/10.7160/eriesj.2020.130305
Boucherie, Sacha. 2018. ‘“Predatory” vs Trustworthy Journals: What Do They Mean for the Integrity of Science?’, Elsevier Connect, https://www.elsevier.com/connect/predatory-vs-trustworthy-journals-what-do-they-mean-for-the-integrity-of-science
Bowman, Deborah E., and Wallace, Michael B. 2017. ‘Predatory Journals: A Serious Complication in the Scholarly Publishing Landscape’, Gastrointestinal Endoscopy, 87.1: 273–74, https://doi.org/10.1016/j.gie.2017.09.019
Brezgov, Stef. 2019. ‘Bogus Journal Accepts Profanity-Laced Anti-Spam Paper’, ScholarlyOA, https://scholarlyoa.com/bogus-journal-accepts-profanity-laced-anti-spam-paper/
Busch, Judith W. 1985. ‘Mentoring in Graduate Schools of Education: Mentors’ Perceptions’, American Educational Research Journal, 22.2: 265, https://doi.org/10.2307/1162843
Christopher, Mary M., and Young, Karen M.. 2015. ‘Awareness of “Predatory” Open-Access Journals among Prospective Veterinary and Medical Authors Attending Scientific Writing Workshops’, Frontiers in Veterinary Science, 2.22: 111–22, doi.org/10.3389/fvets.2015.00022
Clark, Jocalyn. 2018. ‘Letter to the Editor – Predatory Journals: Bad for All But Especially Authors from Low and Middle Income Countries’, Acta Medica Portuguesa, 31.3: 181–85, https://doi.org/10.20344/amp.10489
‘Contact’. [n.d.]. Beall’s List of Potential Predatory Journals and Publishers, https://beallslist.net/contact/
Darbyshire, Philip. 2017. ‘Fake News. Fake Journals. Fake Conferences. What We Can Do’, Journal of Clinical Nursing, 27.9–10: 1727–29, https://doi.org/10.1111/JOCN.14214
Ellis, Henry C. 1992. ‘Graduate Education in Psychology: Past, Present, and Future’, American Psychologist, 47.4: 570–76, https://doi.org/10.1037/0003-066X.47.4.570
Foss, Karen A., and Foss, Sonja K. 2008. ‘Accomplishing the Mission: Creating a Partnership with Your Advisor’, in Getting the Most from Your Graduate Education in Communication: A Graduate Student’s Handbook, ed. by Sherwyn Morreale and Pat Arneson (Washington, DC: National Communication Association), 59–70
Gaff, Jerry G. 2002. ‘The Disconnect between Graduate Education & Faculty Realities’, Liberal Education, 88.3: 6–13
Grudniewicz, Agnes., Moher, David., Cobey, Kelly D., Bryson, Gregory L., Cukier, Samantha and others. 2019. ‘Predatory Journals: No Definition, No Defence’, Nature, 576.7786: 210–12, https://doi.org/10.1038/d41586-019-03759-y
Johnson, W. Brad, and Huwe, Jennifer M. 2002. ‘Toward a Typology of Mentorship Dysfunction in Graduate School’, Psychotherapy, 39.1: 44–55, https://doi.org/10.1037/0033-3204.39.1.44
Koerber, Amy., Starkey, Jesse C., Ardon-Dryer, Karin., Cummins, R. Glenn., Eko, Lyombe and others. 2020. ‘A Qualitative Content Analysis of Watchlists vs Safelists: How Do They Address the Issue of Predatory Publishing?’, Journal of Academic Librarianship, 46.6, https://doi.org/10.1016/j.acalib.2020.102236
Kurt, Serhat. 2018. ‘Why Do Authors Publish in Predatory Journals?’, Learned Publishing, 31.2: 141–47, https://doi.org/10.1002/leap.1150
Larkin, Marilynn. 2018. ‘To Thwart Predatory Publishing, We Need to Work Together’, Elsevier Connect, https://www.elsevier.com/connect/to-thwart-predatory-publishing-we-need-to-work-together#reputable-journal
Leung, Jonathan G., Wieruszewski, Patrick M., Stee, LeAnn., Takala, Christopher R., and Palmer, Brian A. 2020. ‘Predatory Journals: A Cautionary Tale and a Lesson in Copyright Transfer’, Commentary, 95.3: 441–44, https://doi.org/10.1016/j.mayocp.2019.09.001
Manca, Andrea., Cugusi, Lucia and Deriu, Franca. 2019. ‘Questioning the Efficacy of Predatory Journals’ Blacklists’, BJPsych Advances, 25.2: 120–21, https://doi.org/10.1192/BJA.2018.72
Memon, Aamir Raoof., and Waqas, Ahmed. 2017. ‘Indexing by Bibliographic Databases of Journals Published in the Developing World’, Science and Engineering Ethics, 24.4: 1371–75, https://doi.org/10.1007/S11948-017-9898-Y
Mills, David and Inouye, K. 2020. ‘Problematizing “Predatory Publishing”: A Systematic Review of Factors Shaping Publishing Motives, Decisions, and Experiences’, Learned Publishing, 34.2: 89–104, https://doi.org/10.1002/LEAP.1325
Misra, Durga Prasanna., Ravindran, Vinod., Wakhlu, Anupam., Sharma, Aman., Agarwal, Vikas and others. 2017. ‘Publishing in Black and White: The Relevance of Listing of Scientific Journals’, Rheumatology International, 37: 1773–78, https://doi.org/10.1007/s00296-017-3830-2
Neylon, Cameron. 2017. ‘Blacklists Are Technically Infeasible, Practically Unreliable and Unethical. Period.’, Science in the Open, http://cameronneylon.net/blog/blacklists-are-technically-infeasible-practically-unreliable-and-unethical-period/
O’Neil, James M., and Wrightsman, Lawrence S. 2001. ‘The Mentoring Relationship in Psychology Training Programs’, in Succeeding in Graduate School: The Career Guide for Psychology Students, ed. by S. Walfish and A. K. Hess (Mahwah, NJ: Lawrence Erlbaum Associates Publishers), 111–27
Petrie, Trent A., and Wohlgemuth, Elaine A. 1994. ‘In Hopes of Promoting Cohesion among Academics: New and Established’, The Counseling Psychologist, 22.3: 466–73, https://doi.org/10.1177/0011000094223009
Quek, Heng Chuan, and Teo, Eng Kiong. 2018. ‘Predatory Publishing; Pressures, Promotions and Perils’, Proceedings of Singapore Healthcare, 27.1: 3–5, https://doi.org/10.1177/2010105817749602
Rele, Shilpa., Kennedy, Marie and Blas, Nataly. 2017. ‘Journal Evaluation Tool’, LMU Librarian Publications & Presentations, 40, https://digitalcommons.lmu.edu/librarian_pubs/40/
Roberts, Jason. 2016. ‘Predatory Journals: Think before You Submit’, Headache, 56.4: 618–21, https://doi.org/10.1111/HEAD.12818
Ruiter-Lopez, Leon., Lopez-Leon, Sandra and Forero, Diego A. 2019. ‘Predatory Journals: Do Not Judge Journals by Their Editorial Board Members’, Medical Teacher, 41.6: 691–96, https://doi.org/10.1080/0142159X.2018.1556390
Schira, H. Rainer, and Hurst, Chris. 2019. ‘Hype or Real Threat: The Extent of Predatory Journals in Student Bibliographies’, Partnership, 14.1: 1–16, https://doi.org/10.21083/PARTNERSHIP.V14I1.4764
Schlosser, Lewis Z., Lyons, Heather Z., Talleyrand, Regine M., Kim, Bryan S. K. and Johnson, W. Brad. 2010. ‘Advisor-Advisee Relationships in Graduate Training Programs’, Journal of Career Development, 38.1: 3–18, https://doi.org/10.1177/0894845309358887
Shamseer, Larissa., Moher, David., Maduekwe, Onyi., Turner, Lucy., Barbour, Virginia and others. 2017. ‘Potential Predatory and Legitimate Biomedical Journals: Can You Tell the Difference? A Cross-Sectional Comparison’, BMC Medicine, 15.1: 1–14, https://doi.org/10.1186/s12916-017-0785-9
Shrestha, Jiban., Subedi, Subash., Shokati, Behzad and Chaudhary, Amit. 2019. ‘Predatory Journals: A Threat to Scholarly Publishing’, Journal of Education and Research, 8.1: 89–101, https://doi.org/10.3126/jer.v8i1.25482
Teixeira Da Silva, Jaime A. 2013. ‘Predatory Publishing: A Quantitative Assessment, the Predatory Score’, Asian Aust J Plant Sci Biotechnol, 7.1: 21–34, http://www.globalsciencebooks.info/Online/GSBOnline/images/2013/AAJPSB_7(SI1)/AAJPSB_7(SI1)21-34o.pdf
‘Think. Check. Submit’. 2021. Think. Check. Submit., https://thinkchecksubmit.org/
Umlauf, Mary Grace and Mochizuki, Yuki. 2018. ‘Predatory Publishing and Cybercrime Targeting Academics’, International Journal of Nursing Practice, 24.1: 1–7, https://doi.org/10.1111/IJN.12656
Wilde, Judith Busch, and Schau, Candace Garrett. 2014. ‘Mentoring in Graduate Schools of Education: Mentees’ Perceptions’, The Journal of Experimental Education, 59.2: 165–79, https://doi.org/10.1080/00220973.1991.10806559
Wood, Kelly E., and Krasowski, Matthew D. 2020. ‘Academic Email Overload and the Burden of “Academic Spam”’, Academic Pathology, 7, https://doi.org/10.1177/2374289519898858
Wrench, Jason S., and M. Punyanunt, Narissra. 2004. ‘Advisee-Advisor Communication: An Exploratory Study Examining Interpersonal Communication Variables in the Graduate Advisee-Advisor Relationship’, Communication Quarterly, 52.3: 224–36, https://doi.org/10.1080/01463370409370194
Yucha, Carolyn. 2014. ‘Predatory Publishing: What Authors, Reviewers, and Editors Need to Know’, Biological Research for Nursing, 17.1: 5–7, https://doi.org/10.1177/1099800414563378
1 Our Texas Data Repository Dataverse includes a table showing participant demographic information. See https://doi.org/10.18738/T8/QUBMLI (“Participant Occupation and Regional Demographics Table”). All quotations from interviews are reported without correction of grammatical errors or other irregularities. Some quotes were abbreviated using […] to achieve clarity of the original message.
2 Coding to support this chapter’s analysis was conducted in an early phase of the project, at a time when the transcripts had not yet been de-identified. Thus, we have not provided a published dataset specific to this chapter. However, readers may access the published dataset for Chapter 7, available at https://doi.org/10.18738/T8/3RZARP. This published dataset (see “NVivo file paradox theory 12.26.22.nvp”) includes the full text of interview transcripts, de-identified to protect participants’ anonymity, although the coding evident in this file was conducted at a later phase of the project.
3 In recent discourse, new terminology has been suggested instead of blacklists or whitelists, which have problematic symbolism in regard to racial relations. For example, Koerber and others (2020) use the term ‘watchlist’ to refer to lists that aim to identify predatory journals or publishers and ‘safelist’ to refer to lists that aim to identify legitimate journals or publishers. In the study, they highlight the commonalities and differences among the criteria of these lists to understand the broad contours of the controversies that underlie them.